Why You Need This Feature
- Sensitive footage can contain identifiable faces, tactical responses, or private locations, where securing the content is critical.
- In legal, defense, or compliance use cases, the ability to prove file authenticity and manage strict access control is essential.
- FireLight™ provides a field-ready, lightweight solution for end-to-end video protection, even in mobile or remote deployments.
Value and Benefits:
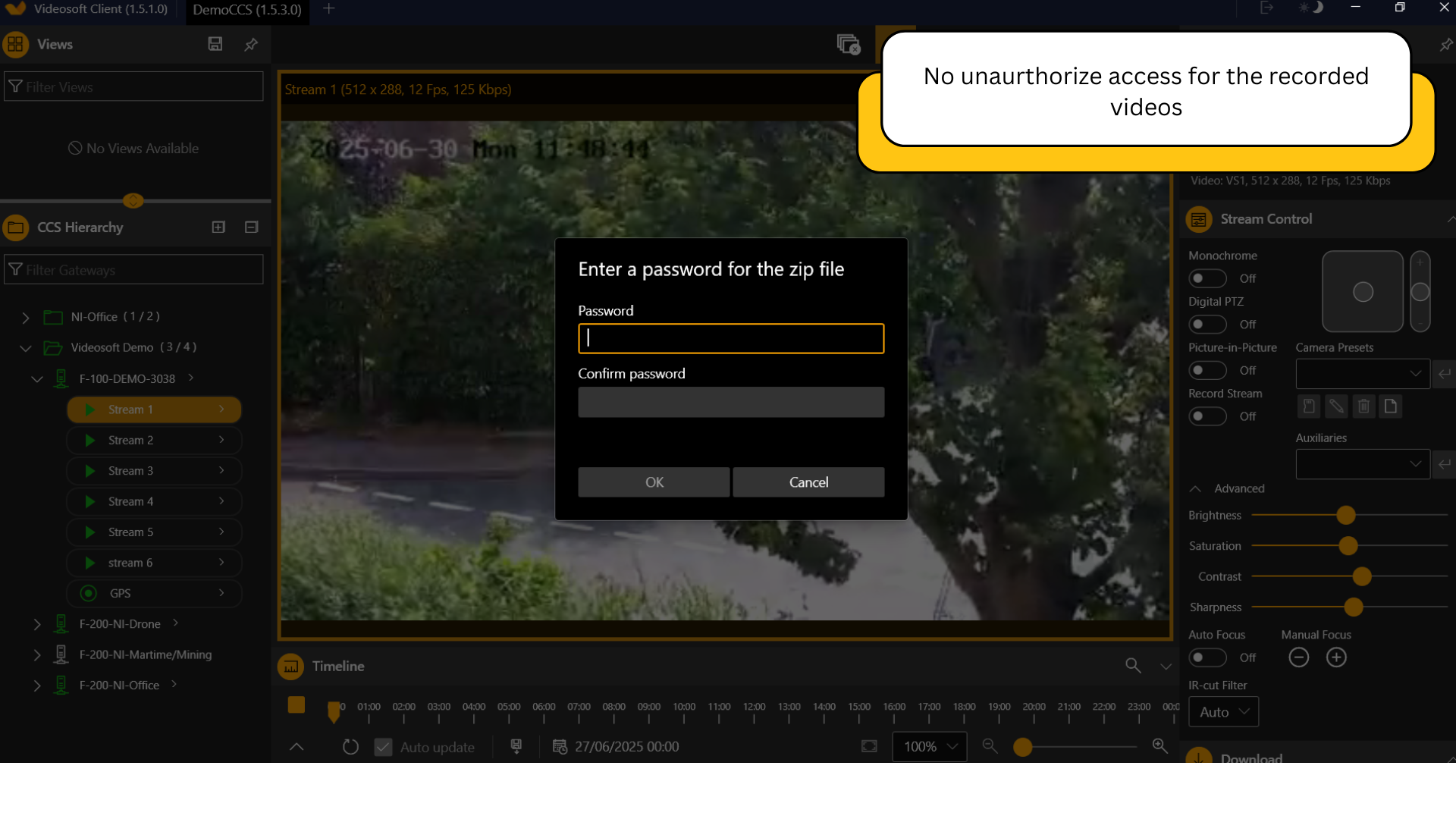
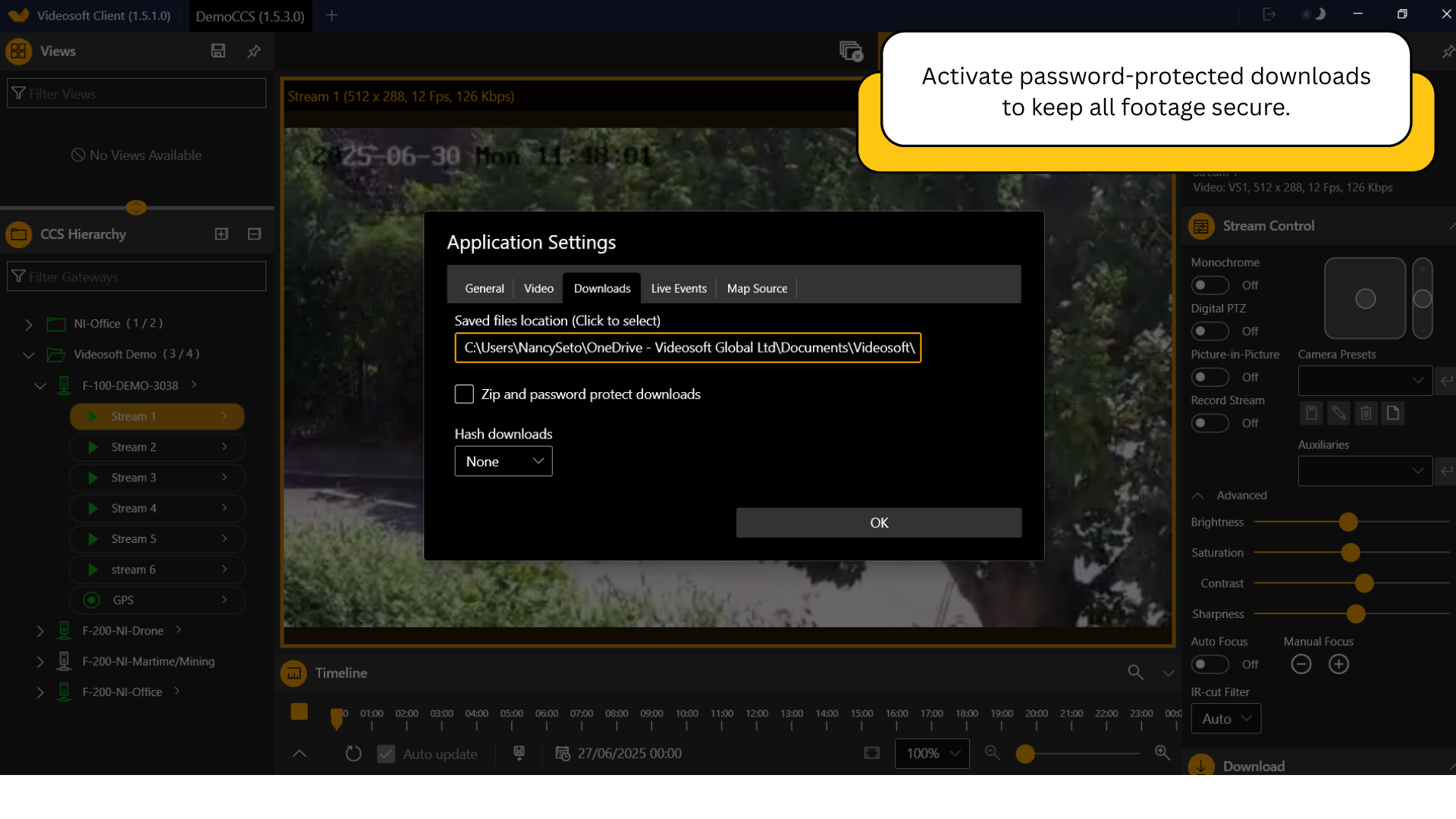
Prevents Unauthorized Access
Password protection ensures only trusted individuals can download and view footage.
Maintains Legal Admissibility
File hashing creates a digital fingerprint, verifying that evidence hasn’t been altered after export.
Enforces Operational Discipline
Role-based controls prevent users from viewing or exporting files that exceed their clearance level.
Supports Remote Teams Securely
Whether sharing footage with HQ or external agencies, you maintain full control over who sees what.
Scalable Across Organizations
From small teams to large-scale multi-agency operations, permission tiers scale with your needs.
Ready to transform your real-time video streaming experience?
Book a live demo, because seeing its capabilities is the best way to understand its full potential.
Frequently Asked Questions
What happens if a download file is shared with someone who doesn’t have access?
If password protection is enabled, they will not be able to access the file.
How does file hashing work in FireLight™?
Each exported file is run through a cryptographic hash function (e.g., SHA-512), creating a unique checksum. This allows you to verify the file hasn’t been modified, deleted, or tampered with after downloading it.
Can different roles be created for different departments or users?
Yes. FireLight™ supports custom role creation, allowing fine-grained permissions across field teams, analysts, command center operators, or third-party investigators.